How malware started a Bitcoin hack that YouTube just can't keep up with
If you've been keeping up with tech news this week, you've likely heard about, or seen first-hand, how several YouTube channels have succumbed to a widespread cyberattack. Over the course of the last week or so, many channels have had their security compromised by attackers, who have taken to broadcasting fake live streams advertising Bitcoin scams. In many ways, the attack echoes a recent breach on Twitter which generated thousands of dollars in scammed Bitcoin after a Twitter employee was paid off to give hackers access.
Whilst the details of the hacks themselves vary slightly, one core theme remains. All of them feel totally let down by YouTube.
Yet the YouTube saga is very different from the recent Twitter breach in a number of ways, most significantly in YouTube's seemingly lax response to the problem. We caught up with three major YouTube creators to find out exactly what happened to their channels, and what happened when they went to YouTube for help. Whilst the details of the hacks themselves vary slightly, one core theme remains. All of them feel totally let down by YouTube.
I spoke with Craig Groshek, director/owner of Chilling Entertainment, and the administrator of Chilling Tales for Dark Nights, an audio horror entertainment channel of more than 1,500 videos and 340k subscribers, about what happened.
Not only was Craig a victim of the hack, but he has also been vocal on Twitter in trying to get help for many of the other creators who have been caught up in the scandal. Two such channels are 'itsAamir', and 'PapaFearRaiser'. Between the two of them, they have nearly two million subscribers. Like Groshek, Aamir, and Jordan (PapaFearRaiser) Antle both had their channels compromised, and they too kindly agreed to share their stories.
What happened?
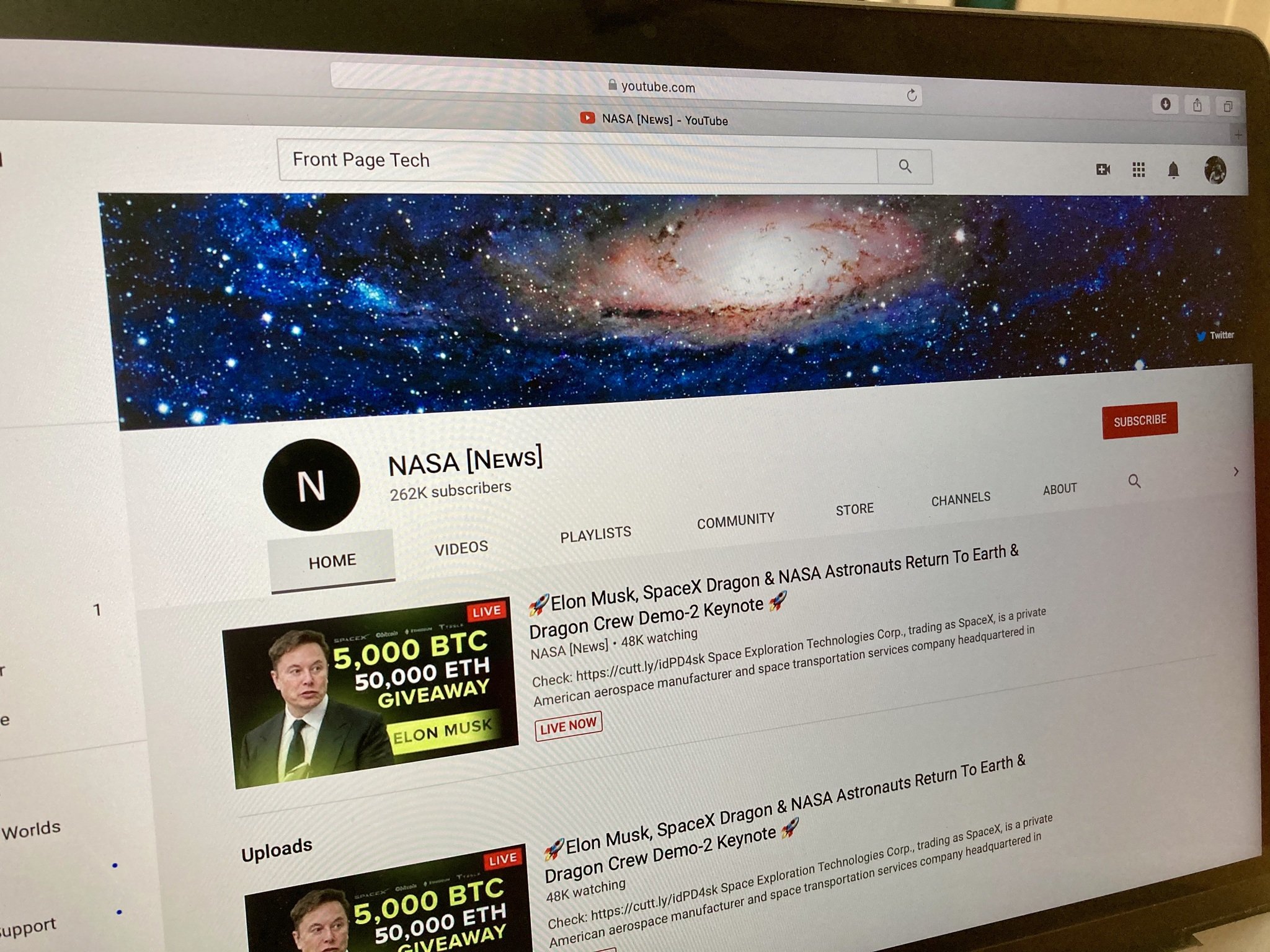
Aamir, Antle, and Groshek all discovered that their YouTube accounts had been compromised over the course of the last couple of weeks. All three channels were found to be broadcasting live Bitcoin scam videos encouraging users to send in Bitcoin to a BTC address with the promise the money would be doubled. The videos looked like the below image. All three also found that most, if not all of their YouTube videos had been made private, and their channels had been rebranded. This was common across all of the hacks we've seen on YouTube.
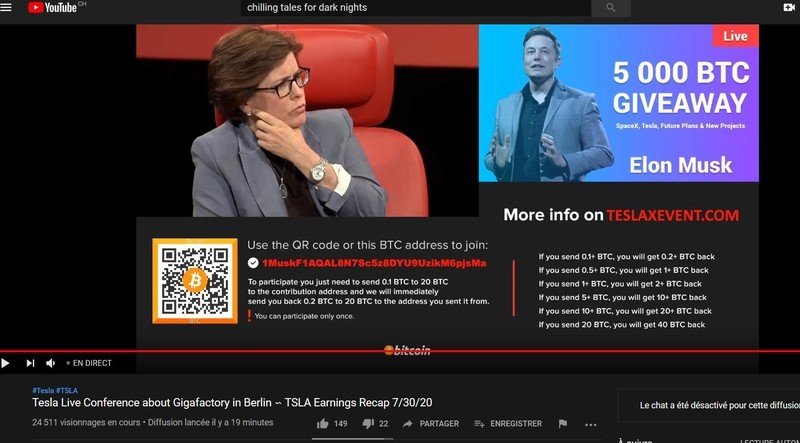
"My channel was compromised on July 29, 2020, at around 4 PM CT," says Groshek. "Hijackers totally bypassed 2FA and did not change my passwords, or attempt to redirect my AdSense. Rather, they set all my videos to private except for three, and put up Bitcoin scams live, and changed my name to Tesla, as well as my logo. They removed all my playlists and channel connections, and emptied my channel description."
Many were quick to cry SIM swapping and some kind of 2FA bypass as some of these hacks unfolded. However, the stories of all three of our creators here reveal a far more sinister mode of operation. In the run-up to their channels being compromised, Aamir, Antle, and Groshek all received emails from companies, purportedly offering them sponsorship deals to plug software on their channels.
Be an expert in 5 minutes
Get the latest news from Android Central, your trusted companion in the world of Android
"Two weeks ago, I got a sponsor email, where I was told to advertise "Resolve 16" video editor on my channel," explains Aamir. Turns out, the email was fake. After speaking first over mail, and then WhatsApp, Aamir was given a download link to the software. Lured in by the seemingly genuine operation, Aamir tried to run the software on his PC, only to be met with an error message, then nothing. At this point, he knew something was amiss.
Antle (PapaFearRaiser) tells a similar story:
I essentially received what appeared to be a "professional" business email. This was someone saying they represented a company called Magix Studios and we're offering me a business opportunity to promote their product. Once I agreed they sent me over the product link to download (which I assumed would be safe as I've done this sort of thing before and it was 100% legit) and once I downloaded the WinRAR file and opened it up, nothing had happened.
Like Aamir, Antle knew something wasn't right about the software he'd just clicked on. Within 60 minutes, his entire YouTube channel had been compromised.
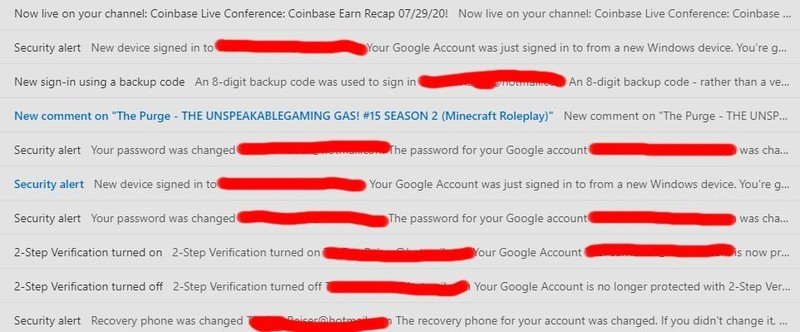
Jordan received a chilling chain of emails stating that the recovery phone had been changed for his channel, then to say that 2FA was turned off, then back on again, then that his password had been changed and a new device had logged in. A backup code was used to sign into the channel, and then another new device alert came through. Finally, he got an email to say that a video titled 'Coinbase Live Conference: Coinbase Earn Recap 07/29/20 was now live on his channel. All within the space of one hour.
Like Groshek and Aamir, all of Antle's videos were made private, and the channel was rebranded as Coinbase Live.
Definitely malware
"Definitely malware". I caught up with Rich Mogull, Security Analyst for Securosis, and CISO for DisruptOps to dissect these stories. "WinRAR files are one of the most common sources" he continues, explaining how hackers could use malware to create connections from a trusted computer to modify password and security settings (including MFA or 2FA) to take control of an account. When you switch off 2FA on Google, you don't get a 2FA prompt to confirm the change, because you've already logged in as a trusted user on a trusted device or browser.
Further suggesting malware, not SIM swapping, was to blame, one of the first messages Antle received was to say his 2FA had been switched off, not that it had been used to sign in to a different device or browser. The stories don't preclude some kind of 2FA, SIM swapping attack (and there are plenty of other compromised creators who might have fallen foul of this), but they do seem to suggest that in these two cases, a malware attack was the primary cause. Windows Defender told Aamir after the fact that the program he had downloaded seemed suspicious, but by then it was too late.
Windows Defender told Aamir after the fact that the program he had downloaded seemed suspicious, but by then it was too late.
Groshek's story is a bit different. Like Aamir and Antle, he got a suspicious email regarding a software sponsorship deal, but after making further inquiries and receiving a software download link, decided not to click on it. He did however notice a screenshot attached to the email. Mogull says this could indicate a "drive-by" malware attack, whereby malware could've been used even without Groshek clicking on the software download link. Mogull further notes that sometimes in the case of a 'drive-by', you don't even have to read the email.
YouTubers are no strangers to getting sponsorship offers by emails, and Antle tells me he's received them before, both real and fake, regarding possible deals for sponsors. The faked emails are a common thread in every single story here, and even though Groshek didn't click on his, it seems likely that getting the follow-up email in the first place might have been enough. There is certainly a chance that the malware, in the course of extracting data from victim's computers could've also picked up phone numbers for a SIM swap, and 2FA by way of SMS remains a pretty shaky way to shore up any online account. But malware seems to have been the prime method used to compromise all three channels of the creators we spoke with.
Dropping the ball
If the way these accounts seem to have been compromised wasn't harrowing enough, YouTube's response was arguably worse.

Aamir tweeted YouTube the night he realized he'd been hacked, and received a DM from TeamYouTube. As with other creators, he was asked to fill out a special form, after which they said someone from the Creator Support Hacking Team would get in touch via email.
If the way these accounts seem to have been compromised wasn't harrowing enough, YouTube's response was arguably worse.
From Aamir's understanding, YouTube has to generate the form and send a hacked creator a special link, after which they have 72 hours to fill it in, only the message that said "We've given you access to this form" contained no such link. As of Thursday, August 6, Aamir had been waiting three days for YouTube to get in touch, after which YouTube simply told him that "the initial process to confirm an account is hacked can take a few weeks" and that they would be in touch. At the time of writing, Aamir's channel is still totally compromised. He is still waiting for a response, his channel videos are all still private, and the channels name is still branded 'Ethereum Foundation [LIVE]'.
Antle tells a similar story. "YouTube was also very painful," he says. "They basically gave deadbeat responses and I was left in the dark for a majority of those 4 days. Their Twitter team did not help much at all and made me feel like my situation wasn't serious when it obviously was. They really didn't make me feel like they had my security in mind."
Thankfully for Antle, someone from YouTube did in fact get back in touch, and his channel has mostly been restored. But he still can't publish videos yet, more on that later…
Groshek too got his channel back, but not without a fight. He told me how YouTube provides "little to no resources to explain how to contact them and get this resolved online", with no mention of Twitter accounts like @TeamYouTube or Google Support forums. "They don't tell you that TeamYouTube are middlemen with no authority", he says, "or that these hacks and hijackings have been going on for years."
Groshek says that his faith in YouTube is so shaken that he plans to leave the platform within the next year.
Groshek says it took a week before anyone from YouTube Creator Support reached out via email, possibly after he posted on Google's Support forums. You can imagine his surprise when he was told that they had no connection with @TeamYouTube and that he would have to provide all of the information to a second department again. Not only that, but neither department could handle the problem directly, and would have to forward the information on to their hijacking team. Groshek described his experience as "abysmal", and that YouTube's handling of the crisis had done more damage to him and the other channels than the hackers. He continues:
"Regardless of whether channel operators "fell for" sophisticated phishing attacks, etc, YouTube needs to recognize they are a primary target for these sorts of attacks, and implement stronger methods of protection to prevent this from happening… They themselves admit it's happening so often they can't keep up.
Groshek says that his faith in YouTube is so shaken that he plans to leave the platform within the next year.
But there's more
It isn't just YouTube's direct interaction with the creators that is questionable. Several times this week, I and other YouTube users have seen fake Bitcoin live streams pushed to our YouTube homepages as recommended videos. You really couldn't make it up.
https://twitter.com/reneritchie/status/1291174178834587649
The aftermath for all the creators, especially Aamir (who still doesn't have his channel back) is extensive. Many creators have lost subscribers as a result of the hacks, 1,200 for Groshek, and more than 10,000 for Antle. Not to mention the loss in ad revenue whilst their channels were compromised, both from videos that were hidden and from not being able to upload.
To add more insult to injury, both Antle and Groshek received Community Violation strikes on their channels due to the Bitcoin scam live streams.
To add more insult to injury, both Antle and Groshek received Community Violation strikes on their channels due to the Bitcoin scam live streams. Despite presumably being aware of the hack, YouTube rejected the appeal of both automatically. In a Tweet, Antle said:
Hey @ytcreators I literally appealed this strike and just like I figured, it got rejected. Can you please get some internal team to help me? This really isn't fair. I'm being punished for getting hacked? pic.twitter.com/AQSlc2CIOuHey @ytcreators I literally appealed this strike and just like I figured, it got rejected. Can you please get some internal team to help me? This really isn't fair. I'm being punished for getting hacked? pic.twitter.com/AQSlc2CIOu— PapaFearRaiser (@TheFearRaiser) August 7, 2020August 7, 2020
To add insult to the insult, YouTube then reset the upload ban penalty on Antle's channel because he had appealed the ruling. He appealed with just four days of the seven-day ban left, but he now has to wait a further seven days before he can upload any videos to his main channel, the first of which will be a warning to his subscribers and the community about his experience.
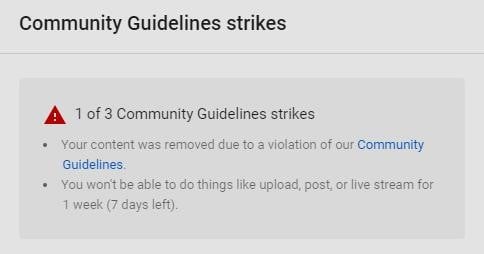
Like Antle, Groshek was unable to post any videos on his Chilling Tales channel until yesterday, August 7. Way to go, YouTube.
Aamir, Antle, and Groshek are not the only creators affected by this. Notably, Apple leaker Jon Prosser had his YouTube channel FrontPageTech compromised. To stop any further damage, the entire FPT channel was removed from YouTube, three days later; they've heard nothing in response.
To recap
The three creators we spoke to are just the tip of the iceberg. As we mentioned earlier, Groshek in particular has vocally criticized YouTube in its handling of dozens of channels who have been hacked in recent days, showing that plenty of other creators have been affected.
Add @AdamDuffArt and @jon_prosser to the list of those hacked by Bitcoin scammers this week. @ctfdn_official, @TheFearRaiser, @AlexHalford, @RecDTRH, @eltito_delfifa, @aamiristhis, & @KhujLeeFamily. How many more need to fall before you do something to stop this, @TeamYouTube? pic.twitter.com/GJY4rTj6ipAdd @AdamDuffArt and @jon_prosser to the list of those hacked by Bitcoin scammers this week. @ctfdn_official, @TheFearRaiser, @AlexHalford, @RecDTRH, @eltito_delfifa, @aamiristhis, & @KhujLeeFamily. How many more need to fall before you do something to stop this, @TeamYouTube? pic.twitter.com/GJY4rTj6ip— Chilling Tales for Dark Nights (@ctfdn_official) August 6, 2020August 6, 2020
Given the nature of the hacks (the Bitcoin live streams, privatizing videos, changing channel names) it seems highly likely that many of these attacks come from the same source. As noted, all three creators we spoke to seem to have been exposed to malware through the promise of software sponsorship deals. Even though only two of the three creators actually downloaded suspicious files, the likelihood of a 'drive-by' attack through the email Groshek received seems to suggest that malware, rather than SIM swapping may have been the primary mode of attack.
It is impossible to say what happened in the many other cases regarding those channels with whom we haven't spoken to, and there is all possibility that many different methods, or perhaps a combination of certain exploits have been used to gain access to these accounts.
The three creators we spoke to are just the tip of the iceberg.
What doesn't seem to be in any doubt, however, is just how poorly YouTube seems to have treated the creators we spoke to. For them and countless others, YouTube is their source of income and livelihood. Yet, when they went to YouTube for help, poor or perhaps no communication, channel strikes for community violations, and rejected appeals against those strikes have left a bitter taste. For Groshek, it was enough to convince him that it was time to leave the platform, it may well convince others.
At the time of writing, Google had not responded to our request for comment on this story.